Zero Trust Security Solutions Powered by Superior Technology
Cymbel’s solutions leverage software and hardware from Palo Alto Networks and other leading cybersecurity vendors.
Cymbel is a long-term strategic partner to Palo Alto Networks, a pioneer of the Zero Trust cybersecurity concept. By leveraging Palo Alto Networks’ best-in-class tools and technologies, we’re able to provide solutions that secure even the most complex network environments.
Palo Alto Networks has been a Gartner Magic Quadrant “Leader” for network firewalls for 8 consecutive years.
Maximize the Benefit of Next-Generation Firewalls
The next-generation firewall (NGFW) is a central aspect of the Zero Trust cybersecurity model. It provides a level of insight and control over network traffic that far exceeds what previous generations of firewall were designed to provide.
We guide organizations through the deployment process of Palo Alto Network’s NGFWs, from the early planning and procurement stage, on through to the regular maintenance you’ll need to ensure long-term stability of your Zero Trust solution.
A documented process for Palo Alto NGFW deployment
Realize Zero Trust Security in any Network Environment
Cymbel can use Palo Alto Networks diverse line of firewall products to enforce zero trust security throughout any network environment, including cloud and containerized environments.
- Help ensure regulatory compliance standards like GDPR, PCI DSS, HIPAA in the cloud with advanced threat prevention capabilities and advanced network segmentation.
- Secure virtual branch offices and software-defined networks and improve the consistency of management efforts with a unified console.
Network Microsegmentation
Building a Zero Trust environment involves careful network microsegmentation, which means logically isolating sensitive workloads and data from each other. Cymbel’s engineering team guides organizations through this process, helping them prevent lateral network activity and reduce the risk of a serious data breach.
The Cymbel team is your guide to the microsegmentation process
- Determine the right model of microsegmentation through risk analysis and threat modeling
- Create plans and policies for each application that is a candidate for segmentation
- Optimize the microsegmentation solution to balance the needs of security and business departments
Centralized Networks Security Management
The security operations at many organizations have become overwhelming. Heterogenous devices — each with their own management consoles — frustrates your teams’ ability to gain insight into cybersecurity incidents and respond effectively.
Palo Alto Network’s Panorama helps organization reduce this complexity. It unifies the management of firewalls and other security functions into a single web-based interface.
Cymbel helps organizations realize full power of their Panorama deployment
- Centralize the management of firewall security policies
- Achieve convenient access to reports, logs, and network traffic information
- Classify traffic based on its type, such as application, user, and content
- Uncover persistent threats anywhere in your network with improved visibility
Zero Trust is Achievable – Just Ask Us How
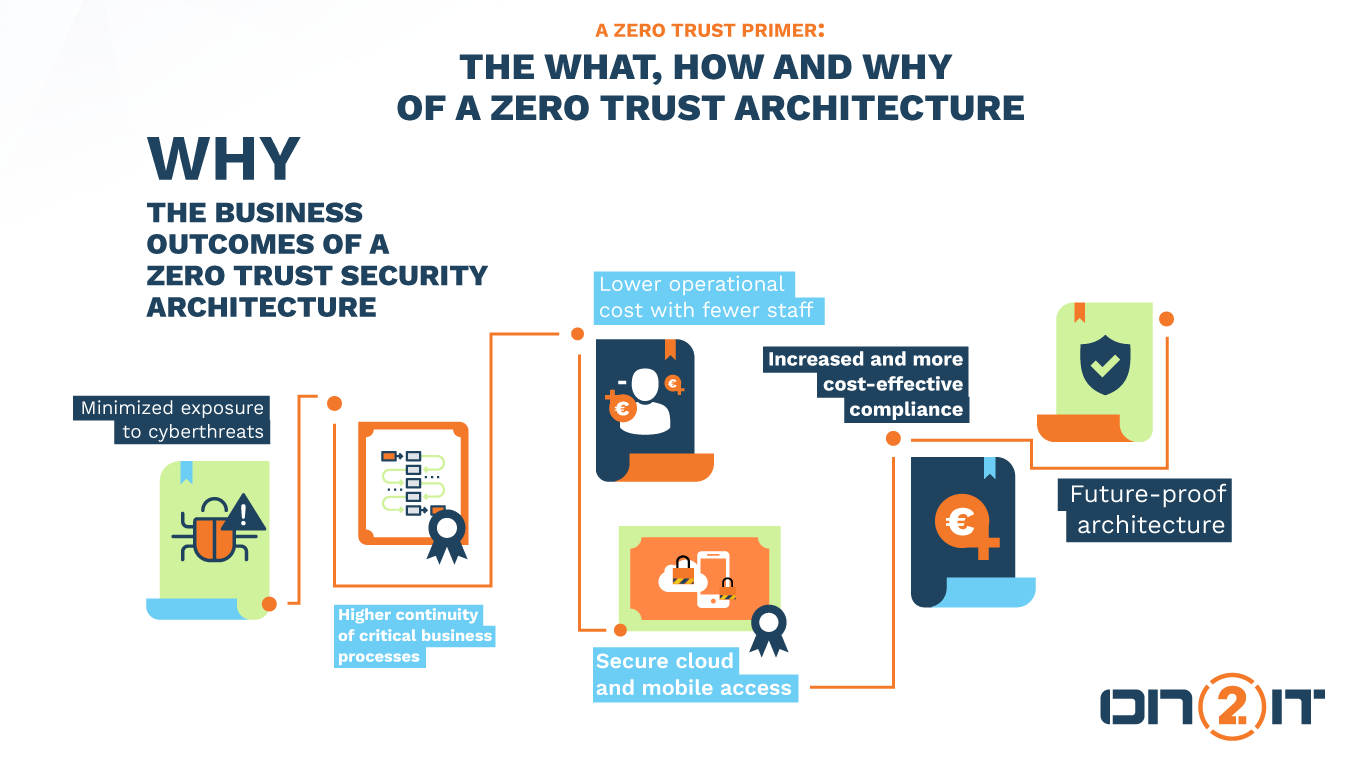
The complexity involved in zero-trust security can be overwhelming, but it doesn’t have to be. With a veteran at your side, any organization can successfully realize the full benefit of Zero Trust security.
If you have a question about Cymbel’s Zero Trust approach and how it can benefit your organization, we’d be happy to help. Contact us any time at sales@cymbel.com.